Security First: Gate.io's Multi-Protection System Safeguards User Funds
Source: Gate.io
In the world of cryptocurrency, security is a core issue. By the end of February 2025, the industry saw a surge in fund theft incidents, once again bringing user asset security into focus.
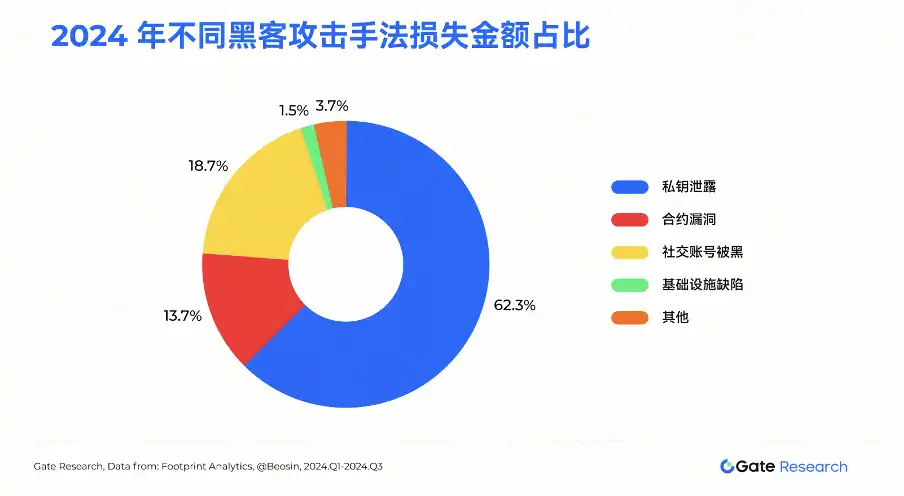
According to a report by the Gate Research Institute, as of November 2024, the blockchain ecosystem had experienced a total of 1,740 publicly disclosed security incidents, resulting in a total loss of $337.44 billion. In 2024 alone, there were 369 incidents, causing a loss of $23.08 billion, highlighting that hacker attacks have become a persistent threat. Particularly, incidents of private key leakage accounted for 62.3% of all losses.
Facing industry challenges, Gate.io has always adhered to the core principle of "security first," and with leading technology and strict risk control systems, has built an unbreakable security barrier for users.
Top-Tier Defense System: Rooting Out Risk from the Source
It is well known that technology is the cornerstone of security. Gate.io understands its importance and has spared no effort in R&D, creating a comprehensive and multi-layered security protection system.
The independently developed trading system is the core of Gate.io's security system. Each module undergoes independent iterations, professional company penetration testing, and annual security audits to ensure that the system remains impregnable in the face of complex attacks. The system's frontend uses protection services from globally leading security companies like Cloudflare and Akamai, building sturdy defenses to keep out malicious traffic and attacks.
In terms of data transmission, Gate.io employs the Transport Layer Security (TLS) protocol to ensure that all website data is not stolen or altered during transmission. This encryption technology is like putting on an "invisible cloak" for user data, making it inaccessible to hackers.
When facing DDoS attacks, through a four-step process of detection, response, crushing, and logging, the platform builds a self-evolving anti-DDoS attack system, continuously improving its response capabilities. Gate.io's anti-DDoS mechanism acts like an intelligent shield, automatically identifying and defending against various attacks.
Additionally, the platform concurrently deploys a Web Application Firewall (WAF) and DNS security measures to further enhance overall defense capabilities. The WAF can intelligently identify and block illegal intrusions, data tampering, and vulnerability attacks, while DNS security measures effectively prevent the possibility of hijacking or fraudulent communication.
Rigorous Internal Control: Building a Robust Safety Net
No matter how powerful the technology, it still requires airtight internal management safeguards. Gate.io believes that internal security is a crucial part of the overall platform security system. Therefore, the platform adopts the strictest security measures to ensure that every aspect is under constant monitoring.
All computers are equipped with endpoint protection mechanisms and are fully protected by corporate firewalls. At the same time, the platform establishes a zero-trust security architecture, following the principle of "continuous validation, never trust," to ensure security protection. It ensures that the software is always up to date, follows the principle of least privilege (PoLP) and role-based access control (RBAC), regularly reviews and detects redundant account access, strictly enforces access permission application procedures, ensures that only authorized personnel can access sensitive data, and fundamentally reduces security risks.
Development management is also a key part of internal control. Gate.io has established a comprehensive Software Development Life Cycle (SDLC) management system, strictly controlling the software's security quality throughout its entire lifecycle, including software requirement design, architecture review, development, continuous integration, continuous deployment, and software operation and maintenance. During the software development process, strict code audits are conducted on developers' code submissions, and testing technologies such as SAST, SCA, and DAST are introduced to continuously detect any backdoor code and security vulnerabilities. This rigorous management process eliminates potential security vulnerabilities from the source and builds an impenetrable defense line for platform security.
Account Security: Two-Factor Authentication, Bulletproof Accounts
For users, account security is the most concerning issue, and Gate.io has spared no effort in this regard. The login process is the first line of defense for account security. Gate.io provides various verification methods such as SMS, Google OTP, IP address monitoring, and email to ensure the authenticity of user identity. The dual protection mechanism of login password and fund password provides double security for the account, further strengthening the defense.
In the transaction and withdrawal process, every withdrawal requires multiple security authentications, including SMS or email verification. After password resets and other security setting changes, users are unable to withdraw funds within 24 hours, effectively preventing the possibility of hackers extracting funds by tampering with security settings.
In addition, Gate.io also provides users with a security log function, allowing users to view their account's login and operation records at any time. Once any anomalies are detected, immediate countermeasures can be taken.
Asset Protection: Dual Protection of Cold and Hot Wallets, Fortifying Funds
In the world of digital assets, the security of a wallet is directly related to the security of the user's assets. Gate.io adopts a cold-hot wallet separation approach to provide users' assets with "double protection."
The hot wallet uses various advanced technologies such as multi-signature, TEE (Trusted Execution Environment), MPC (Secure Multi-Party Computation), threshold signatures, and big data risk control to ensure the security of private keys. All user deposit and withdrawal requests must undergo multi-risk management authentication before being broadcast to the blockchain for confirmation to prevent fund risks.
The cold wallet follows the principles of off-site backup, bank custody, multiple storage media, multi-signature, and complete offline storage to ensure the absolute security of assets. Through many years of practical experience, Gate.io has established a sound management process and emergency response mechanism. The "cold-hot wallet separation" management approach maximizes the security of user assets.
Asset Reserve: World's Leading 100% Reserve Scale
Through Merkle Trees and Zero-Knowledge Proof (zk-SNARK) technology, Gate.io has achieved transparent verification of a 100% reserve scale.
As of January 17, 2025, Gate.io's total reserve value reached $10.328 billion, with a reserve ratio as high as 128.58%, significantly surpassing industry standards. The platform's reserve covers over 200 types of user assets, with an excess reserve scale of $2.296 billion and an excess reserve ratio of 28.58%, representing a $450 million increase compared to December last year, a growth rate of 24.38%.
At the same time, Gate.io regularly releases reserve data and undergoes audits by the authoritative blockchain security company Hacken to ensure the transparency and security of the reserve.
Smart Contracts: A "Sharp Eye" for Security Audits
The security of smart contracts is one of the pain points in the blockchain industry. Gate.io adopts a "zero-tolerance" attitude in this regard, providing automated contract audits, real-time monitoring of on-chain events, and ensuring contract risks are manageable.
Furthermore, Gate.io rigorously selects quality projects, conducts regular security audits, and signs non-malfeasance agreements with project teams, actively monitoring the teams' performance. Through comprehensive security measures, Gate.io provides solid security for smart contracts, effectively preventing potential risks.
Bug Bounty Program: Global White Hat Support
In the security field, vulnerabilities are often the biggest threat. Therefore, Gate.io has established a bug bounty program to encourage security researchers to report potential security vulnerabilities on the platform. Through this mechanism, Gate.io can promptly discover and patch potential security issues, further enhancing the platform's security.
The Vulnerability Reward Program is an important supplement to Gate.io's own security system. It not only enhances the platform's protection capabilities but also attracts a large number of security researchers to pay attention to and participate, allowing Gate.io to establish a good reputation in the security field of the cryptocurrency industry, earning widespread trust and support.
Industry Benchmark: Building a Comprehensive Security Solution
Gate.io's security system is dedicated to the centralized exchange field, providing users with multidimensional security through decentralized solutions such as Gate Chain and Block Info.
Gate Chain focuses on user asset security and decentralized trading. With its innovative online hot insurance account and liquidation protection system, it effectively addresses core industry issues such as asset theft and key loss. On the other hand, Block Info provides encrypted asset data and analysis services to official institutions, exchanges, and financial institutions to help them track illicit asset flows.
This comprehensive security solution has enabled Gate.io to reach new heights in the security field. Gate.io not only safeguards user asset security but also sets a security benchmark for the entire industry.
With Security as Faith, Building the Cornerstone of Trust
Through a series of hardcore security measures, Gate.io has built an impregnable "iron wall" for users. From technical guidance to internal control, from account protection to asset protection, from compliance transparency to smart contracts, and to the vulnerability reward program and comprehensive security solution, Gate.io always pursues the ultimate in security.
Looking ahead, Gate.io will continue to strengthen technological innovation, improve its security system, and provide users with a more secure, reliable, and transparent trading environment. Gate.io's goal is to ensure that every user can trade with peace of mind and make "security" synonymous with Gate.io.
Disclaimer: This content does not constitute any offer, solicitation, or advice. You should always seek independent professional advice before making any investment decisions. Please note that Gate.io may restrict or prohibit all or part of its services from certain restricted areas. Please read the user agreement for more information.
This article is contributed content and does not represent the views of BlockBeats.
You may also like

Mastercard Launches Agent Pay for AI, Plans to Record AI Agent Payment Authorizations on Polygon
Mastercard launched Agent Pay for AI, a new payment protocol designed to help AI agents make small payments such as pay-per-use access to data and APIs. The system plans to record human-granted AI agent permissions on Polygon, focusing on verifiable authorization, identity, and payment controls.

Curve Deploys Llamalend v2 on Optimism With 250,000 OP Incentives
Curve launched Llamalend v2 on Optimism with 250,000 OP incentives from the Optimism Foundation. The upgrade expands Llamalend beyond its earlier crvUSD-focused model, adding broader collateral support, LlamaRisk market reviews, and the ability to use Curve LP tokens as collateral.

Raydium Old Liquidity Pool Reportedly Exploited, With $1.34 Million Moved to Ethereum and Tornado Cash
An old Raydium liquidity pool was reportedly exploited for around $1.34 million in USDC, RAY, and wSOL, with the stolen funds bridged to Ethereum and deposited into Tornado Cash. The incident highlights the tail risks of legacy DeFi pools, old contracts, and cross-chain fund laundering paths.

Kalshi Executive Challenges “SBF Backed AI Unicorns” Narrative, Says Leopold Aschenbrenner Was Key Figure
Kalshi executive John Wang questioned the “SBF backed AI unicorns” narrative, saying Leopold Aschenbrenner was the key figure behind major AI investment decisions.

Pantera Capital Partner: How Tokenization is Restructuring the Private Equity and Early Investment Ecosystem?

New York Proposes Stricter Stablecoin Issuer Rules Aligned With Federal GENIUS Act
NYDFS proposed stricter stablecoin issuer rules aligned with the GENIUS Act, covering reserves, custody, redemption timelines, audits, and capital buffers.

Every exchange is a "Universal Exchange."

The counterattack of traditional finance: Alliance chains are quietly reviving

CryptoQuant Says Bitcoin Profitable Supply Is Near 45% Pressure Zone as On-Chain Data Points to Market Repricing
CryptoQuant said Bitcoin’s profitable supply is nearing the 45% pressure zone, signaling rising market stress, unrealized losses, and a possible on-chain repricing phase.

Bitcoin Falls Below 200-Week Moving Average as On-Chain Data Shows Over Half of Supply in Loss
Bitcoin dropped below its 200-week moving average as on-chain data showed over 50% of circulating supply is now in loss, signaling rising market stress.

CFTC Reportedly Plans New Prediction Market Rules Focused on Manipulation Risk and Public Interest Review
The CFTC is reportedly preparing new prediction market rules focused on manipulation risk, public interest review, and retail trader protections.

Meet the new WEEX trial fund—your gateway to greater profits

WEEX Labs Lands at Dutch Blockchain Week: A Disruptive Crypto × AI Conversation Sets Sail in Amsterdam

SK Hynix Reportedly Plans U.S. ADR Listing as Early as August, With SEC Approval Possible in Late June
SK Hynix may pursue a U.S. ADR listing as early as August, with SEC approval reportedly possible in late June amid strong AI chip supply chain demand.

SpaceX vs Tesla vs xAI: Which Elon Musk Trade Has the Biggest Upside in 2026?

OpenAI Reveals It Has Confidentially Submitted an S-1 to the SEC, Keeping the Door Open for a Future IPO
On June 9, according to an OpenAI announcement, the company recently confidentially submitted a draft S-1 registration statement to the U.S. Securities and Exchange Commission (SEC), beginning the preliminary compliance process for a potential initial public offering. OpenAI said it chose to disclose this proactively because it expected the news might leak; however, the company has not yet set a specific listing timeline, and related arrangements may still take some time.

Latest research from 13 top universities including Cornell University: The current state, challenges, and misconceptions of the fusion of Crypto and AI

Deconstructing Anthropic: The Best AI Company, Possibly Also a Type of Organizational Invention
Mastercard Launches Agent Pay for AI, Plans to Record AI Agent Payment Authorizations on Polygon
Mastercard launched Agent Pay for AI, a new payment protocol designed to help AI agents make small payments such as pay-per-use access to data and APIs. The system plans to record human-granted AI agent permissions on Polygon, focusing on verifiable authorization, identity, and payment controls.
Curve Deploys Llamalend v2 on Optimism With 250,000 OP Incentives
Curve launched Llamalend v2 on Optimism with 250,000 OP incentives from the Optimism Foundation. The upgrade expands Llamalend beyond its earlier crvUSD-focused model, adding broader collateral support, LlamaRisk market reviews, and the ability to use Curve LP tokens as collateral.
Raydium Old Liquidity Pool Reportedly Exploited, With $1.34 Million Moved to Ethereum and Tornado Cash
An old Raydium liquidity pool was reportedly exploited for around $1.34 million in USDC, RAY, and wSOL, with the stolen funds bridged to Ethereum and deposited into Tornado Cash. The incident highlights the tail risks of legacy DeFi pools, old contracts, and cross-chain fund laundering paths.
Kalshi Executive Challenges “SBF Backed AI Unicorns” Narrative, Says Leopold Aschenbrenner Was Key Figure
Kalshi executive John Wang questioned the “SBF backed AI unicorns” narrative, saying Leopold Aschenbrenner was the key figure behind major AI investment decisions.
Pantera Capital Partner: How Tokenization is Restructuring the Private Equity and Early Investment Ecosystem?
New York Proposes Stricter Stablecoin Issuer Rules Aligned With Federal GENIUS Act
NYDFS proposed stricter stablecoin issuer rules aligned with the GENIUS Act, covering reserves, custody, redemption timelines, audits, and capital buffers.

